Top Ways to Secure your Mobile Apps
- 22 December, 2021
- Reading Time: 6 mins
What is mobile app security, and why do we need it?
Mobile applications are quickly becoming the primary way for consumers to interact with businesses. Unfortunately, a lot of them are easily compromised because they lack basic security features. This makes it easy to bypass using freely available tools and basic reverse engineering techniques.
Building a secure app is critical to maintaining trust with customers and protecting your brand’s reputation. By enabling security best practices, you can ensure that your apps stand up against growing external threats, such as hacking attacks.
Mobile application data security can be divided into three layers – the mobile application layer, the backend layer, and the communication channel layer. In this blog, we will explore security best practices for the mobile application layer and the communication channel layer.
How to enable Best Security Practices for Mobile Apps
Follow these practices at each stage of mobile app development, to ensure that your applications are equipped with the best security mechanisms:
DATA AT REST:
Data at Rest refers to the mobile app data stored in the application sandbox.
Secure your credentials: Sometimes you need a secure place to store small chunks of data like passwords or certificates. Both iOS and Android provide a secure data storage space called Keychain/Keystore that encrypts all of its content on the device and prevents other apps from extracting those keys.
Access minimal resources: Access only the bare minimum resources on the device, whichever ones are mandatory. Always ensure that your app is not seeking permissions to resources that aren’t being used.
Encrypt your data: Encrypt the sensitive data stored on mobile applications, such as Strings. Use techniques like end-to-end encryption, HMAC, hashing, symmetric encryption, and asymmetric encryption.
Be careful while collecting Personally Identifiable Information (PII) data: Avoid gathering PII from the users unless it is absolutely necessary for your business. GDPR compliance is one such compliance that protects PI data from getting stored in the application when not required.
Follow Firebase Security Rules: Firebase Security Rules leverage extensible, flexible configuration languages to secure data in Cloud Firestore, Firebase Realtime Database, and Cloud Storage. Firebase Security Rules stand between your data and malicious users. You can write simple or complex rules that protect your app’s data to a very granular level, specific to what the app requires.
Secure the information in your logs: Avoid logging sensitive information like PII data, health data, financial data, or passwords.
Restrict clipboard access: Control clipboard access to prevent copy and paste functions.
DATA IN TRANSIT:
Mobile applications typically communicate with the backend servers to fetch data. This helps in fetching large amounts of data without storing it locally and also helps to keep synchrony between other platforms that consume the same data, like web portals.
1) Secure communication channels: HTTPS communications should be secured with TLS. Transport Layer Security, or TLS, is a widely adopted security protocol designed to facilitate privacy and data security for communications over the Internet. A primary use case of TLS is encrypting the communication between applications and servers. This can be achieved by SSL Pinning your mobile app by including a list of valid certificates (or its public keys or its hashes) in your app bundle. The app can, therefore, check if the certificate used by the server is on this list. This ensures that not only the OS but even your app trusts this certificate.
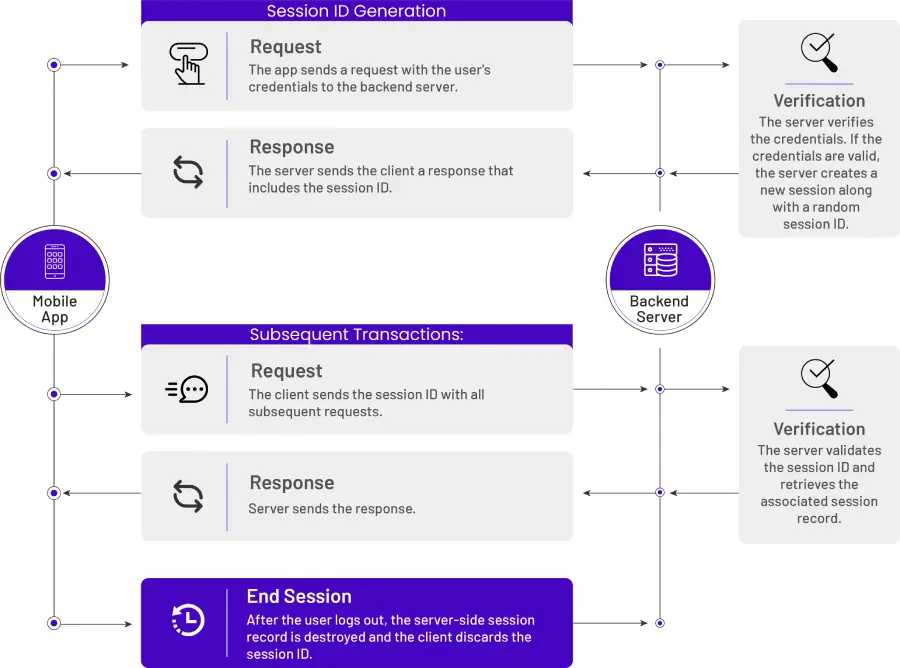
2) Proper session management:To transact between the application and backend server, mobile apps use session tokens. To maintain trust, mobile apps first authenticate the user through the backend. In response to successful authentication, the server issues a session cookie to the mobile app. Below is the optimal flow for how session management should be handled for maximum mobile app security:
Excerpt From: Bernhard Mueller, Sven Schleier, Jeroen Willemsen, and Carlos Holguera. “OWASP Mobile Application Security Verification Standard 1.3.” Apple Books.
APP RELEASE MECHANISM:
After a mobile application is developed, we come to the stage where it is bundled and shared for testing and release. Developers should secure the bundling and sharing mechanism as it can be a source of data breaches.
1. Code obfuscation:
With Code obfuscation, we can prevent codes from being copied and used without permission. It also helps make your app’s functional logic and algorithms less exposed and makes it harder for attackers to find vulnerabilities in your code. Code Obfuscation methods are as follows:
- Bitcode Obfuscation in iOS applications: Bitcode is the intermediate representation of your source code in the process of compiling it and converting it into machine code.
- Enabling ProGuard in Android applications: ProGuard optimizes the bytecode, removes unused code instructions, and obfuscates the remaining classes, fields, and methods with short names. The obfuscated code makes your APK difficult to reverse engineer, which is especially valuable when your app uses security-sensitive features, such as licensing verification.
2. App Distribution:
Mobile applications should be shared via secured channels like Firebase app distribution or Testflight. No third party app sharing mechanism, such as Diawi, should be used.
3. OWASP Security Standards:
OWASP Mobile Application Security Verification Standards (OWASP Foundation | Open Source Foundation for Application Security) are open source standards which help build smarter mobile services and applications. It also helps understand the standards and security requirements of any application and defines Levels (L1 and L2). As per the OWASP standards, the Level of the application identified helps in defining the degree of security:
“Implementing the requirements of MASVS L2 increases security, while at the same time increasing cost of development and potentially worsening the end-user experience (the classical trade-off). In general, L2 should be used for apps whenever it makes sense from a risk vs. cost perspective (i.e., where the potential loss caused by a compromise of confidentiality or integrity is higher than the cost incurred by the additional security controls). A risk assessment should be the first step before applying the MASVS.”
4. Developer Guidelines for Security Practices:
a) Android Developer Guidelines: The Android Developer document provides a list of best practices for application security. This should be followed to preserve user trust and device integrity. Major highlights of the best security practices documents are:
- Use implicit intents and non-exported content providers
- Ask for credentials before showing sensitive information
- Apply network security measures
- Use WebView objects carefully
- Use intents to defer permissions
- Share data securely across apps
- Store private data within internal storage
- Store data in external storage based on the use case
- Store only non-sensitive data in cache files
- Use SharedPreferences in private mode
- Check the Google Play services security provider
- Update all app dependencies
b) iOS Developer Guidelines: The iOS Developer document provides a list of best practices for application security.
- Establish a user’s identity (authentication) and then selectively grant access to resources (authorization).
- Secure data, both on disk and in motion across a network connection.
- Ensure the validity of the code to be executed for a particular purpose.
Conducting a Security Audit of live apps and implementation of security practices in ongoing applications is highly recommended for users as well as brands to maintain a user’s trust and the value of the product.
Are you looking for a secured mobile application for your business app? Contact us today to learn more.