Born Secure: Are Security Misconfigurations Compromising your Product’s Security?
- 8 November, 2021
- Reading Time: 6-8 Minutes
-
Overview
There are a number of ways in which a software’s security could be jeopardized. The statement in itself is quite generic in nature, making it more frightening. But, what if we said there are ways to make your upcoming product, platform, or application entirely secure? Quite heart-warming. Yes, there are a few basic approaches to make your program more secure over time if the security concerns are addressed from the start of software development. When developing your system, it’s all about knowing the threats and anticipating the vulnerabilities in your application. Understanding vulnerabilities risk factors before they happen is more important than correcting security breaches after they occur, especially in the case of applications that deal with sensitive information, like education platforms or banking and finance apps.
Returning to where we began, OWASP Top 10 is a list of the top 10 security risks that can be used to minimize or in some cases eliminate the danger of attacks on any web application. Insecure default configurations, incomplete or random configurations, not configuring HTTP headers, or displaying sensitive information unknowingly via error messages are some of the most typical issues in web applications. Your technology development team may take these vulnerabilities for granted and file them away to be dealt with later, sometimes after production deployment. It is sometimes handled and sometimes left unaddressed because neither tests nor developers see any malfunction or functionality challenge in their application. OWASP states that “Not only must all operating systems, frameworks, libraries, and applications be securely configured, but they must be patched/upgraded in a timely fashion.”
Let’s explore how security misconfigurations can affect any software and how they can be taken care of.
-
The Risks Posed by Security Misconfigurations
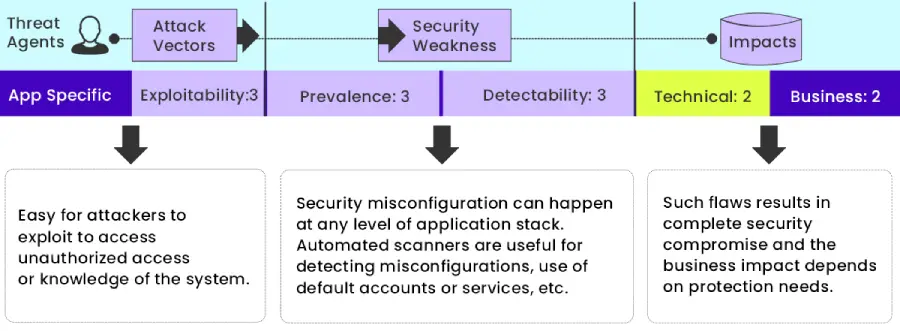
The image below demonstrates the OWASP’s risk rating methodology.
Source: https://owasp.org/www-project-top-ten/2017/A6_2017-Security_Misconfiguration
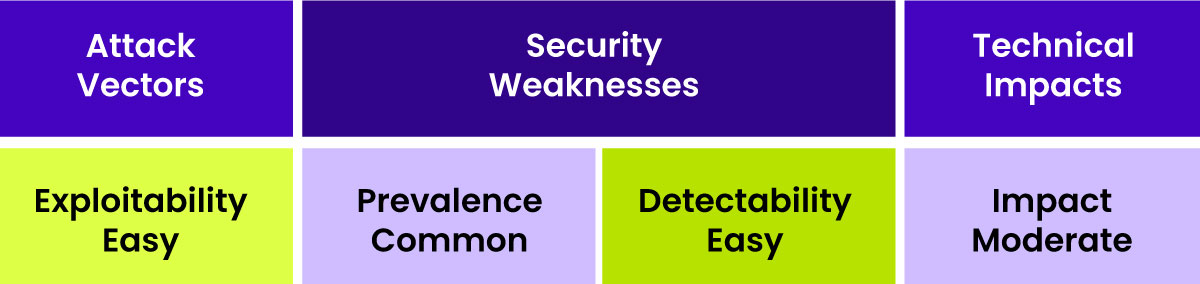
In simpler terms, this means…
So, first and foremost, the standard matrix. Attack Vectors are a type of vulnerability that attacks extremely straightforwardly. It’s also quite common, owed in part to the fact that it is a fairly widespread threat. These are easy to detect.
The impact is moderate, and its severity is determined by the nature of the Security Misconfiguration, given this is such a broad danger. Because this is a broad risk, we must speak extensively about how the Security Misconfiguration risk is exploited. It usually boils down to an attacker gaining access to an unsafe resource. And an insecure resource can range from a poorly secured admin page to unsecured web logs or even internal air communications, thus there are many distinct forms of Security Misconfiguration.
When a website is exposed to this danger, it usually responds by exposing a “gateway risk,” as we refer to it. What we mean by gateway risk is that it’s not the same as, for example, SQL Injection, where the server immediately delivers the attacker the data they want; rather, what’s being given here is information that the attacker can use to exploit other flaws. Let’s have a look at what they might appear to be.
-
Factors that Lead to Security Attacks
Some examples of Security Misconfiguration in product and platform development are shown below.
Out of Date Software
Is your existing software in need of an update? This includes the operating system, web servers or application servers, database servers, programs, and code libraries and packages. When organizational software or systems are out of date, they become more susceptible. We typically find that earlier versions of frameworks do not stack up in terms of robustness. Over the years, technology and development frameworks have subsequently grown and been hardened and more guarded against today’s online threats.
Unnecessary Features
Another good example is the enablement of unnecessary features. Is it really necessary to have every potential service operating on all of a website’s default ports? Maybe you don’t need FTP, or maybe you do. That’s the kind of thing you want to turn off if it’s not in use because that means one less possible attack vector.
Default Accounts and Passwords
Default accounts and passwords that appear to be self-evident. This occurs frequently on physical devices, such as routers, but it also occurs with third-party software applications. This is something to be extremely wary of. There are a number of lists circulating about what the default credentials are for various products.
Immature Error Handling
This is low-hanging fruit for an attacker. One of the most typical occurrences is websites revealing internal implementation data. So, when an exception occurs, and an attacker can easily induce a website to throw an exception, does that give internal information such as the code location or lines of code? In some cases, it even discloses information like credentials used to access databases in some circumstances. Make sure that internal implementation data stays internal.
Security Settings within the Application
Finally, there are some basic security choices available. The majority of web frameworks provide several options for securing the technological environment. Let’s try to condense these into three typical defenses.
-
Ways to Defend Against Security Attacks
Here are some main areas where you can concentrate your efforts to mitigate the risk of Security Misconfiguration.
Hardening the Install
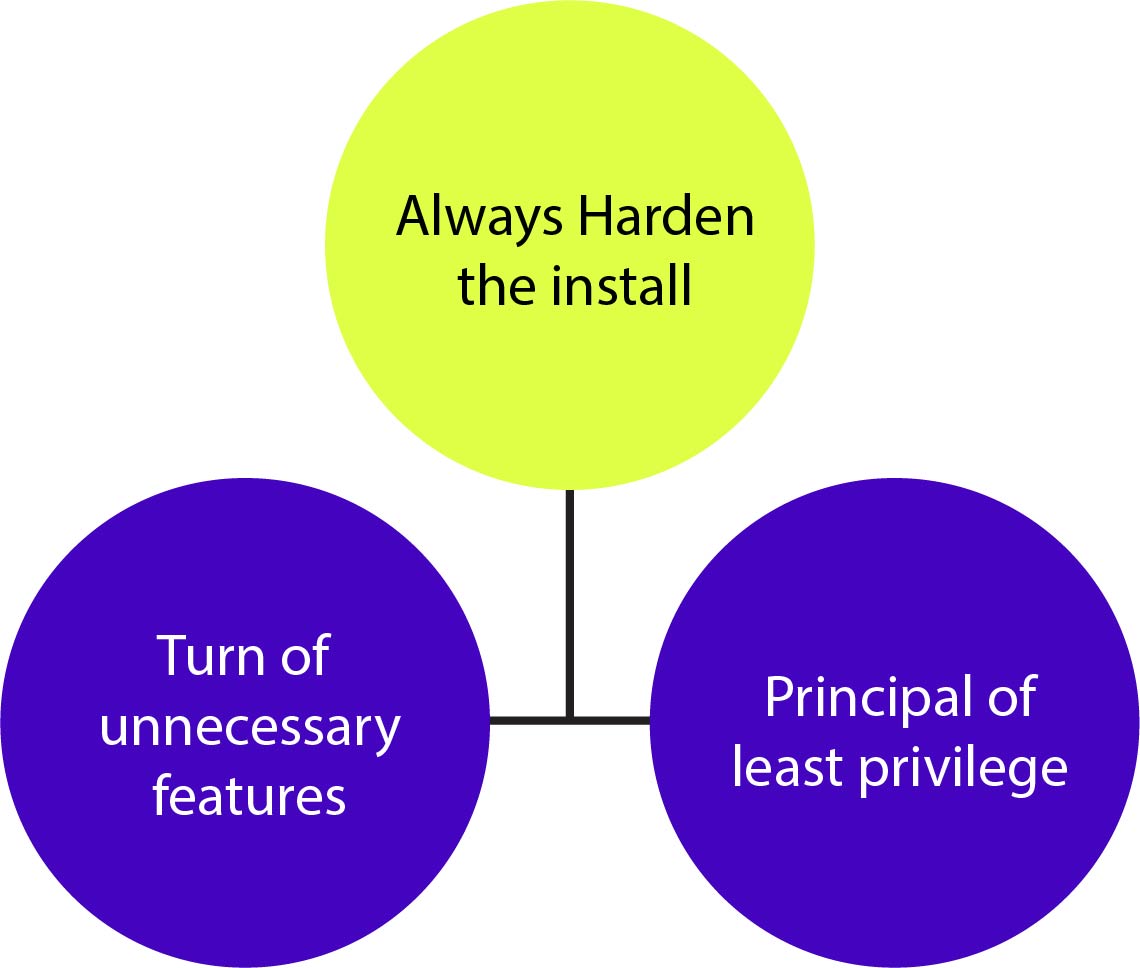
The first is to ensure that the installation is hardened at all times. It’s not just about the web-based application; it’s also about the web server, and we’re talking about things like turning off non-essential functionalities. So, for instance, do you really need directory browsing enabled on your website? This makes it very easy for an attacker to access the file system and start compiling a profile of information. It’s imperative that the “principle of least privilege” be followed at all times. What does the account under which the website is run have the ability to do? Is it possible for it to gain access to other accounts on the server? Is it able to access the files of the operating system?
Tuning the Application Configurations
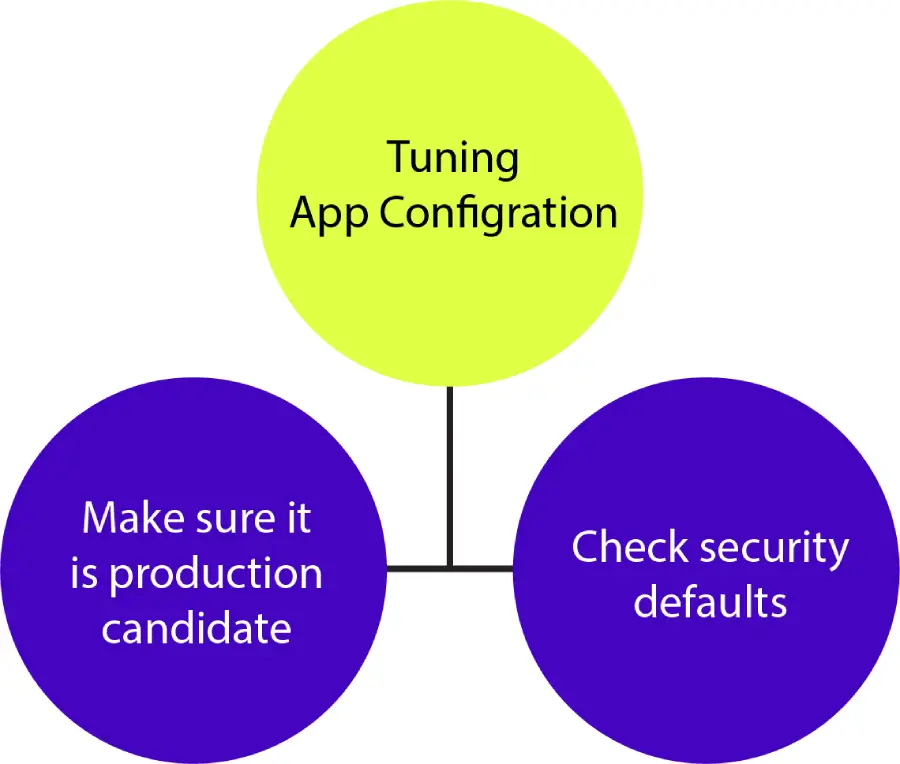
Second, fine-tune the security settings of the app. Many times, we find that the app in the production environment is configured as if it were operating in a development environment for debugging purposes, such as revealing internal errors or allowing debugging tools to access the site. This is not the way a live website should be stored up. It should be avoided at all costs. Also keep in mind that, due to your unique situation, the security defaults in a web application’s configuration are almost certainly not appropriate for your project. Many frameworks allow you to choose the maximum size of allowed requests. It may default to a few megabytes. Is allowing someone to send a few megabytes of data to your website truly necessary? If you cut that number to a few hundred thousand, your chances of a denial of service attack are greatly reduced.
Update Packages and Libraries
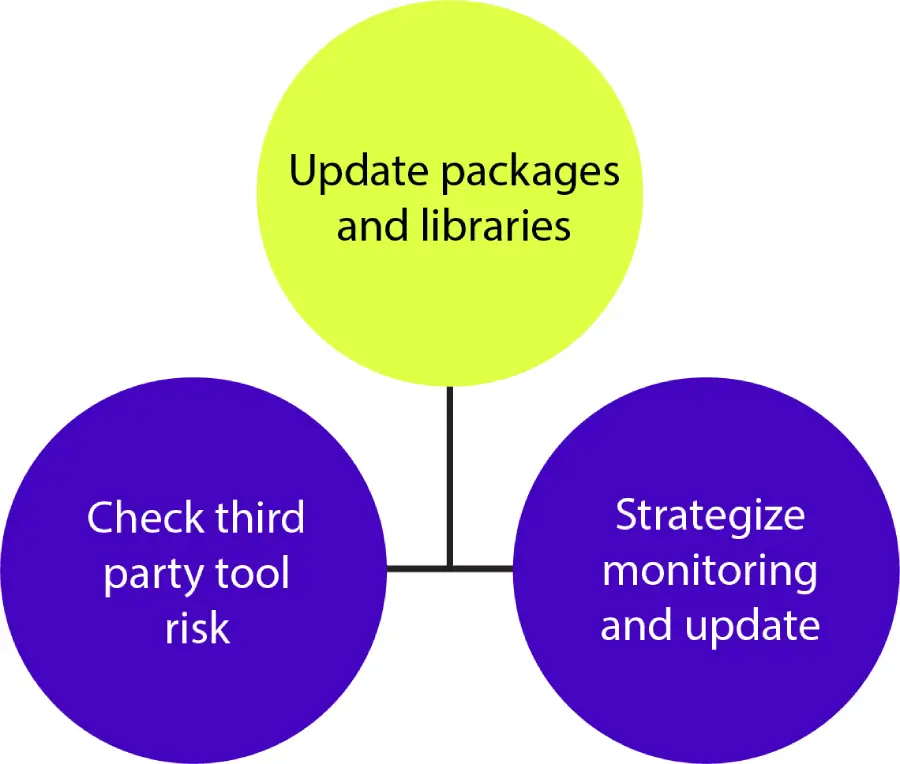
Finally, all of the packages must be brought up to date. Third-party tools should be avoided if possible or utilized with caution. You should be aware of the potential security implications of the third-party tool, and have a system in place to monitor and update them. Depending on your framework, package management can be done in a variety of ways. How do you know when a third-party dependence is vulnerable, and how do you update it? On the other hand, do you have programs that rely on a slew of out-of-date dependencies that are dozens of versions out of date? This is a rather popular attack vector.
-
Building a Secure Technology Ecosystem
Misconfigurations can often be disastrous when it comes to security breaches. In this post, we defined security misconfigurations and the types of attacks that can result if they are not addressed. Having a strong defense system is essential not just for treating misconfigurations but also for the overall ecosystem of the application. We learned about all the defenses that may be used to mitigate the risk of security misconfigurations in any application. Now you know how to do your part to keep your security safe!
To know more about securing your upcoming application or strengthening your organization’s existing platforms, speak to the team at Magic.
Sources
OWASP Top 10
Web Security and the OWASP Top 10: The Big Picture