We are education technology experts.
Explore solutions by your segment
Tap into over 30 years of expertise for transformative digital learning.
We shape learning solutions with your goals in mind. Whether it’s the adoption of AI across enterprises or driving inclusive experiences, see how we’ve helped our clients at different stages of their learning product journey.
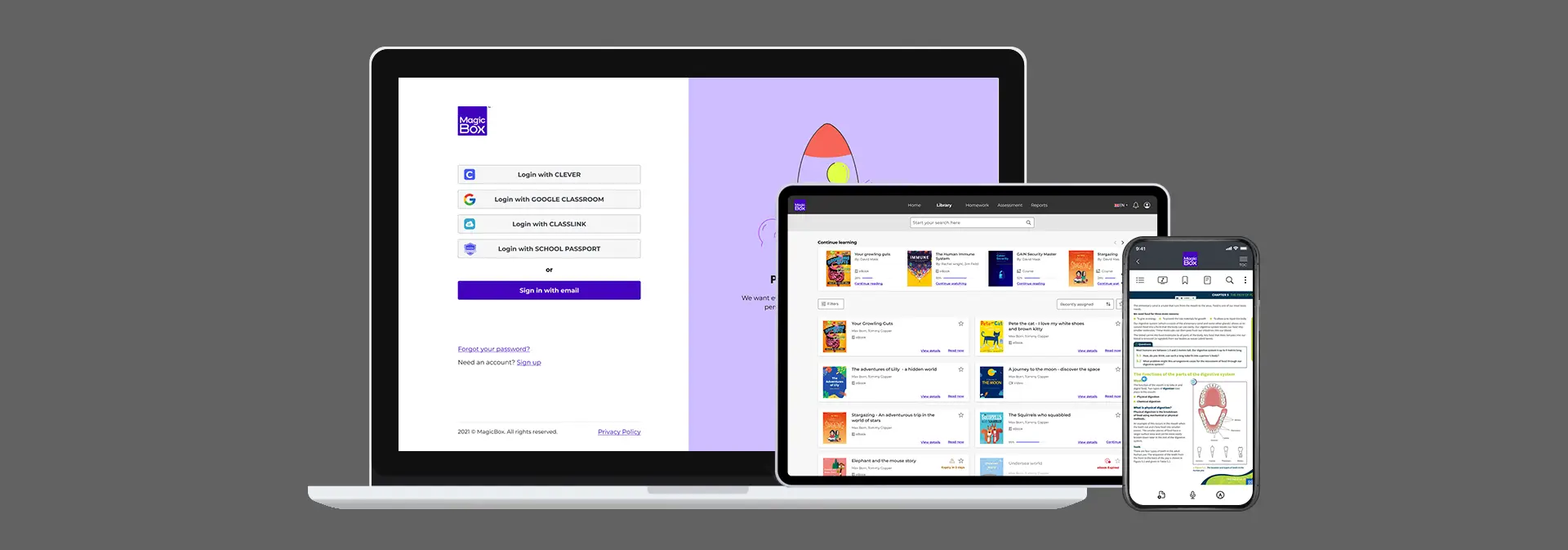
MagicBox is your go-to platform for delivering digital learning seamlessly. Improve your learning product adoption when you choose MagicBox.
Clients served over the past three decades. Find out what keeps them coming back to us.

Speak to our team to learn more about how we can assist with your learning initiatives.